Introduction
Phishing attacks have become a major threat in our digital world. They can happen to anyone, from individuals to large corporations. Understanding phishing attacks is crucial because they can lead to devastating consequences, including identity theft and financial loss. In my own experience as a tech-savvy entrepreneur, I’ve seen firsthand how easily someone can fall victim to these deceptive schemes.
When I first started my online business, I received an email that looked like it was from my bank. It had the bank’s logo and even used my name. The email urged me to click a link to verify my account information. Luckily, I had done my homework on understanding phishing attacks and recognized it as a scam. But many people aren’t as fortunate, and that’s what makes this topic so important.
In this blog post, we’ll dive deep into understanding phishing attacks, how to recognize phishing scams, and effective phishing prevention tips that can help you stay safe online. By the end of this article, you’ll be equipped with the knowledge you need to protect yourself and your loved ones from these malicious threats.
What is Phishing? Understanding Phishing Attacks
Phishing is a term that refers to a type of cybercrime where attackers attempt to trick individuals into revealing sensitive information, such as usernames, passwords, and credit card numbers. Understanding phishing attacks is essential for anyone who uses the internet. It’s not just about knowing what they are; it’s about recognizing how they operate and the tactics used by cybercriminals.
The Evolution of Phishing Attacks
Phishing attacks have evolved significantly over the years. Initially, they were simple emails sent out to thousands of people, hoping that a few would fall for the bait. I remember receiving my first phishing email back in the early 2000s. It was a poorly written message claiming I had won a lottery I never entered. The email was riddled with grammatical errors and looked sketchy. However, as technology advanced, so did the sophistication of these scams.
Today, understanding phishing attacks means recognizing that they can come in many forms—email, SMS (known as smishing), or even voice calls (vishing). Attackers have become incredibly skilled at mimicking trusted sources, making it harder for individuals to distinguish between legitimate communications and scams. They often use social engineering techniques to create a sense of urgency or fear.
For example, I once received an urgent email supposedly from my internet service provider, warning me that my account would be suspended unless I verified my information immediately. The email looked authentic, but thankfully, I had learned about recognizing phishing scams.
The Role of Social Engineering in Phishing
Social engineering plays a significant role in understanding phishing attacks. This technique involves manipulating people into divulging confidential information by exploiting psychological triggers. Attackers often create messages that evoke emotions like fear or excitement to prompt quick action without careful thought.
For instance, during tax season, scammers ramp up their phishing attempts by sending emails that appear to be from tax authorities. These emails often claim there’s an issue with your tax return and urge you to click on a link to resolve it. Understanding phishing attacks means being aware of these seasonal trends and knowing how to spot them.
Types of Phishing Attacks
- Email Phishing: This is the most common type where attackers send fraudulent emails that appear to be from reputable sources.
- Spear Phishing: Unlike generic phishing attempts, spear phishing targets specific individuals or organizations, often using personal information to make the attack more convincing.
- Whaling: This is a more targeted form of spear phishing aimed at high-profile individuals like executives or important personnel within an organization.
- Vishing: Voice phishing involves phone calls where attackers impersonate legitimate entities to extract sensitive information.
- Smishing: Similar to vishing but conducted via SMS messages.
- Pharming: This technique redirects users from legitimate websites to fraudulent ones without their knowledge.
Understanding these different types of phishing attacks can help you identify potential threats more effectively. For example, when I started receiving calls from someone claiming to be from my bank asking for my account details, I immediately recognized it as vishing because I had educated myself on these tactics.
Phishing attacks is not just about knowing what they are; it’s about recognizing their evolution and the various forms they take in today’s digital landscape. By being aware of social engineering tactics and familiarizing yourself with different types of attacks, you can better protect yourself against these threats.
How Do Phishing Attacks Work?
Understanding how phishing attacks work is crucial in today’s digital landscape. These attacks rely on a combination of technology and psychological manipulation to deceive victims. By breaking down the mechanisms used by attackers, you can better equip yourself to recognize and avoid these threats.

Mechanisms Used by Attackers
Phishing attacks typically start with an email or message that appears to come from a trusted source. This could be your bank, a popular online service, or even a colleague. The goal is to create a sense of trust so that you feel comfortable taking the desired action, which usually involves clicking a link or providing personal information.
In my early days as an entrepreneur, I received an email that seemed to be from a well-known software provider I used. The message informed me that my subscription was about to expire and urged me to click a link to renew it. The email included the company’s logo and even addressed me by name, making it seem legitimate. However, I had learned about understanding phishing attacks, so I didn’t click the link. Instead, I went directly to the company’s website and logged in to check my account status. It turned out the email was a phishing attempt.
Impersonation of Trusted Entities
One of the most effective tactics in phishing is impersonation. Attackers often spoof email addresses or create websites that closely resemble legitimate ones. For example, they might use an address like “support@yourbank-secure.com” instead of “support@yourbank.com.” This small change can easily go unnoticed by someone who isn’t vigilant.
Recognizing phishing scams involves being aware of these subtle differences. I’ve encountered several emails where the sender’s address looked almost identical to the real one but had minor variations, such as extra letters or different domains. Always double-check the sender’s email address before taking any action.
Types of Phishing Attacks
- Email Phishing: As mentioned earlier, this is the most common form where attackers send mass emails designed to lure victims into providing sensitive information.
- Spear Phishing: This type targets specific individuals or organizations using personalized information gathered from social media or other sources.
- Whaling: A more sophisticated form of spear phishing aimed at high-profile targets like CEOs or CFOs within a company.
- Vishing: Voice phishing involves phone calls where attackers impersonate legitimate organizations to extract personal information.
- Smishing: This involves sending fraudulent SMS messages that trick users into clicking malicious links.
- Pharming: This technique redirects users from legitimate websites to fraudulent ones without their knowledge, often by exploiting vulnerabilities in browsers or DNS servers.
Urgent Calls to Action
Phishing emails often contain urgent calls to action designed to provoke immediate responses without careful consideration. For instance, an email might state that your account will be suspended unless you verify your information within 24 hours. This sense of urgency can cloud judgment and lead individuals to act impulsively.
I recall receiving an email claiming my online payment account had been compromised and that I needed to verify my identity immediately. The urgency was palpable, but because I understood phishing attacks, I took a step back and contacted customer support through official channels instead of clicking any links in the email.
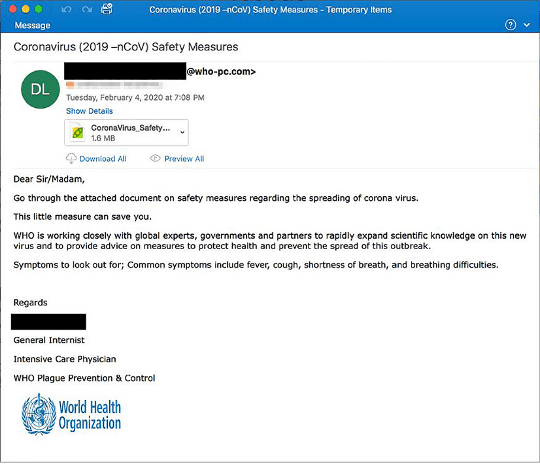
Examples of Real Phishing Emails
To truly understand how phishing works, it helps to look at real examples. Many people have shared their experiences online, detailing how they were targeted and what red flags they missed. Websites like PhishTank allow users to report and view examples of phishing attempts. In one case, an individual received an email that appeared to be from their HR department, asking them to confirm their bank details for payroll processing. The email was convincing, but it contained grammatical errors and a suspicious link that led to a fake login page—classic signs of phishing.
Knowing how phishing attacks work is vital for anyone navigating the digital world today. By recognizing the mechanisms used by attackers—such as impersonation and creating urgency—you can better protect yourself against these threats. Always approach unsolicited communications with caution and verify their authenticity before taking any action.
What Are the Common Signs of Phishing Scams? Recognizing Phishing Scams
Recognizing phishing scams is crucial for protecting yourself and your loved ones from the devastating consequences of these attacks. While phishing attempts have become increasingly sophisticated, there are still common red flags that can help you identify them. By being aware of these signs and educating yourself on recognizing phishing scams, you can significantly reduce your risk of falling victim to these malicious schemes.
Red Flags in Emails and Messages
One of the most obvious signs of a phishing attempt is poor grammar and spelling errors in the message. Legitimate organizations typically have their communications proofread before sending them out. If an email is riddled with mistakes, it’s a good indication that it’s not from a reputable source.
I remember receiving an email that claimed to be from a major tech company I used. The message was full of grammatical errors and used generic greetings like “Dear customer” instead of my name. This immediately raised red flags for me, and I didn’t engage with the email further. Another common red flag is the use of generic greetings. Legitimate organizations will typically address you by name in their communications. If an email starts with “Dear user” or “Dear member,” it’s likely a phishing attempt.
Suspicious Links and Attachments
Phishing emails often contain links or attachments that lead to malicious websites or contain malware. Hovering over a link without clicking it can reveal the actual URL, which may be different from what’s displayed in the email. If the link looks suspicious or doesn’t match the sender’s domain, it’s best to avoid clicking it.
I once received an email that claimed to be from my bank, asking me to click a link to verify my account information. However, when I hovered over the link, I noticed it was a strange URL that didn’t match my bank’s website. I immediately deleted the email and contacted my bank directly to report the incident. Attachments can also be used to deliver malware in phishing attacks. If an email contains an unexpected attachment or one that doesn’t match the sender’s typical communications, it’s best to avoid opening it. Instead, contact the sender through official channels to verify its authenticity.
Examples of Real Phishing Emails
Seeing real-world examples of phishing emails can help you better recognize these scams in the future. Many organizations and websites share examples of phishing attempts to raise awareness and help people identify these threats. One example is an email that appeared to be from a popular online retailer, informing the recipient that their account had been compromised. The email urged the recipient to click a link to reset their password. However, the link led to a fake website designed to steal the user’s login credentials.
Another example is an email claiming to be from a government agency, offering a tax refund. The email contained a link that led to a malicious website asking for personal information. Recognizing phishing scams like these can help you avoid falling victim to similar attempts.
Techniques Used by Attackers
Phishing attackers often use social engineering techniques to create a sense of urgency or fear. They may claim that your account has been compromised or that you’re entitled to a refund, hoping to prompt a quick response without careful consideration.
I remember receiving an email that claimed my online payment account had been hacked. The message used alarming language and stated that I needed to verify my identity immediately to secure my account. However, when I contacted customer support directly, they confirmed that the email was a phishing attempt and that my account was safe.
Recognizing phishing scams is an essential skill in today’s digital landscape. By being aware of common red flags, such as poor grammar, generic greetings, and suspicious links or attachments, you can significantly reduce your risk of falling victim to these attacks. Educating yourself on real-world examples and the techniques used by attackers can further enhance your ability to identify and avoid phishing attempts.
What Are the Consequences of Falling for Phishing Attacks?
Falling victim to a phishing attack can have serious and far-reaching consequences. Understanding these potential impacts is crucial for anyone navigating the digital landscape. By knowing what could happen if you or someone you know gets caught in a phishing scam, you can better appreciate the importance of recognizing phishing scams and implementing effective phishing prevention tips.
Potential Impacts on Individuals
- Financial Loss: One of the most immediate consequences of falling for a phishing attack is financial loss. Attackers often seek to steal credit card information, bank account details, or login credentials to drain accounts or make unauthorized purchases. I remember a friend who clicked on a phishing link, unknowingly providing her credit card details. Within hours, her account was emptied, and she faced a long battle with her bank to recover the lost funds.
- Identity Theft: Phishing attacks can lead to identity theft, where attackers use stolen personal information to impersonate victims. This can result in fraudulent loans, credit card applications, and other financial transactions in your name. The emotional toll of dealing with identity theft can be overwhelming, as it often requires extensive time and effort to resolve.
- Loss of Sensitive Information: Beyond financial data, phishing attacks can also compromise sensitive personal information such as Social Security numbers, medical records, or login credentials for various accounts. This information can be sold on the dark web or used for further malicious activities.
- Emotional Distress: Falling victim to a phishing attack can lead to significant emotional distress. Victims may feel embarrassed, anxious, or violated after realizing they’ve been deceived. I’ve spoken with individuals who experienced panic attacks after discovering unauthorized transactions on their accounts due to phishing scams.
Consequences for Organizations
- Data Breaches: For businesses, the consequences of falling victim to a phishing attack can be catastrophic. A successful attack can lead to data breaches that expose sensitive customer information. This not only affects the organization’s reputation but also leads to legal repercussions and potential fines.
- Financial Loss: Organizations can suffer substantial financial losses due to phishing attacks. This includes costs associated with investigating the breach, notifying affected customers, and implementing additional security measures. In some cases, businesses may face lawsuits from affected customers.
- Reputation Damage: Trust is paramount in business relationships. A successful phishing attack can damage an organization’s reputation and erode customer confidence. Customers may choose to take their business elsewhere if they believe their data is not secure.
- Operational Disruption: Phishing attacks can disrupt day-to-day operations as organizations scramble to respond to breaches and secure their systems. This disruption can lead to decreased productivity and lost revenue.
Real-Life Examples of Phishing Consequences
The consequences of falling for phishing attacks are not just theoretical; there are numerous real-life examples that highlight the severity of these incidents:
- In 2016, a well-known email service provider fell victim to a massive phishing scheme that compromised millions of user accounts. The attackers gained access to sensitive user data, leading to widespread identity theft and financial fraud.
- A large healthcare organization experienced a data breach due to a successful phishing attack that exposed sensitive patient records. The organization faced hefty fines and legal action while also dealing with the fallout from affected patients.
The consequences of falling for phishing attacks can be severe and far-reaching, impacting both individuals and organizations alike. From financial loss and identity theft to reputational damage and operational disruption, understanding these potential impacts emphasizes the importance of recognizing phishing scams and implementing effective phishing prevention tips.
By educating yourself about the risks associated with phishing attacks, you empower yourself to take proactive steps toward safeguarding your personal information and that of your organization.
How Can You Protect Yourself? Phishing Prevention Tips
Protecting yourself from phishing attacks is essential in today’s digital landscape. With cybercriminals becoming increasingly sophisticated, understanding effective phishing prevention tips can make a significant difference in your online safety. In this section, I’ll share practical strategies that you can implement to safeguard your personal information and avoid falling victim to these malicious schemes.
Best Practices for Individuals
- Verify Sender Information: Always check the sender’s email address before taking any action. Phishing emails often come from addresses that closely resemble legitimate ones but have slight variations. For example, an email claiming to be from your bank might come from “support@yourbank-secure.com” instead of “support@yourbank.com.” If something feels off, trust your instincts and verify the sender through official channels. In my experience, I once received an email that appeared to be from a popular online payment service. The sender’s address looked almost identical to the real one, but I noticed a small typo. Instead of clicking the link, I logged into my account directly through the official website and found no alerts or issues.
- Use Multi-Factor Authentication (MFA): Enabling multi-factor authentication adds an extra layer of security to your accounts. Even if a cybercriminal manages to obtain your password, they would still need a second form of verification—like a text message or authentication app—to access your account. This simple step can significantly reduce the risk of unauthorized access.
- Regularly Update Passwords: Changing your passwords regularly and using strong, unique passwords for each account can help protect you from phishing attacks. Avoid using easily guessable information, such as birthdays or common words. Instead, consider using a password manager to generate and store complex passwords securely. I’ve found that using a password manager not only helps me create strong passwords but also saves time when logging into various accounts. It’s a small investment that pays off in peace of mind.
- Be Cautious with Public Wi-Fi: Public Wi-Fi networks can be breeding grounds for cybercriminals looking to intercept sensitive information. Avoid accessing sensitive accounts or entering personal information while connected to public Wi-Fi. If you must use it, consider using a Virtual Private Network (VPN) to encrypt your internet connection.

Organizational Strategies
- Employee Training and Awareness Programs: Organizations should invest in regular training sessions to educate employees about recognizing phishing scams and understanding the risks associated with them. Role-playing exercises and real-life examples can help employees identify potential threats. In my own business, we conduct quarterly training sessions where we simulate phishing attempts to test our team’s awareness. This proactive approach has helped us catch potential threats before they escalate into real issues.
- Implementing Security Software Solutions: Utilize security software that includes anti-phishing features to help detect and block phishing attempts before they reach users’ inboxes. Regularly updating this software ensures that it can effectively combat new threats as they emerge.
- Regular Security Audits and Assessments: Conducting regular security audits helps organizations identify vulnerabilities in their systems and processes. By addressing these weaknesses, businesses can better protect themselves against phishing attacks and other cyber threats.
Staying Informed About New Threats
Phishing tactics are constantly evolving, so staying informed about new threats is crucial for effective prevention. Follow cybersecurity blogs, subscribe to newsletters, and participate in online forums where you can learn about the latest phishing trends and tactics used by attackers. I make it a point to stay updated on cybersecurity news because it helps me anticipate potential threats and adjust my strategies accordingly. Knowledge is power when it comes to protecting yourself from phishing attacks.
Implementing effective phishing prevention tips is vital for safeguarding your personal information in today’s digital world. By verifying sender information, using multi-factor authentication, regularly updating passwords, being cautious with public Wi-Fi, and educating yourself about new threats, you can significantly reduce your risk of falling victim to phishing attacks. Taking proactive steps not only protects you but also contributes to a safer online community for everyone.
What to Do If You Fall Victim to a Phishing Attack?
Realizing that you’ve fallen victim to a phishing attack can be a shocking and distressing experience. However, it’s crucial to act quickly and methodically to mitigate the damage. In this section, I will outline the immediate steps you should take if you suspect that you’ve been compromised, as well as how to recover from such an incident.
Immediate Steps to Take After a Breach
- Change Your Passwords: The first thing you should do is change the passwords for any accounts that may have been compromised. Use strong, unique passwords that you haven’t used before. If you have enabled multi-factor authentication (MFA) on your accounts, make sure it is active and functioning properly. I remember a time when I received a notification from my email provider about suspicious activity on my account. I immediately changed my password and enabled MFA, which provided me with peace of mind. Even though I was stressed, taking swift action helped me regain control.
- Secure Your Other Accounts: If you use the same password across multiple accounts (which you shouldn’t!), change those passwords as well. Attackers often try to access other accounts using the same credentials. This is why having unique passwords for each account is so important.
- Monitor Your Financial Accounts: Check your bank and credit card statements for any unauthorized transactions. If you notice anything suspicious, report it to your bank or financial institution immediately. They can help you freeze your accounts or issue new cards if necessary. After one of my friends fell victim to a phishing scam, she noticed several unauthorized charges on her credit card within days. She contacted her bank right away, which helped her recover most of the lost funds and prevent further unauthorized transactions.
- Notify Relevant Institutions: If the phishing attack involved sensitive information—like your Social Security number or banking details—notify the relevant institutions immediately. For example, if your bank account was compromised, inform your bank so they can monitor for fraudulent activity.
Reporting the Incident
- Report to Authorities: In many countries, there are specific agencies dedicated to handling cybercrime reports. In the U.S., for instance, you can report phishing attempts to the Federal Trade Commission (FTC) at reportfraud.ftc.gov. This helps authorities track down cybercriminals and prevent future attacks.
- Notify Your Employer: If you fall victim to a phishing attack at work, inform your employer or IT department immediately. They may need to take additional steps to secure company data and prevent further breaches.
- Use Reporting Tools: Many email providers allow users to report phishing attempts directly from their inboxes. Use these tools to help combat phishing scams and protect others from falling victim as well.
Long-Term Recovery Steps
- Consider Identity Theft Protection Services: If sensitive personal information was compromised, consider enrolling in an identity theft protection service. These services monitor your personal information and alert you of any suspicious activity related to your identity.
- Place a Fraud Alert on Your Credit Report: Contact one of the three major credit bureaus (Experian, TransUnion, or Equifax) and request a fraud alert on your credit report. This makes it harder for identity thieves to open new accounts in your name.
- Review Your Credit Report Regularly: Keep an eye on your credit report for any unfamiliar accounts or inquiries that could indicate identity theft. You can obtain a free credit report annually from each of the major credit bureaus at AnnualCreditReport.com.
- Educate Yourself About Future Threats: Use this experience as a learning opportunity. Educate yourself about recognizing phishing scams and other cyber threats so that you’re better prepared in the future.
Falling victim to a phishing attack can be overwhelming, but taking immediate action can help mitigate the damage and protect your personal information moving forward. By changing passwords, monitoring financial accounts, reporting incidents, and considering long-term recovery strategies like identity theft protection services, you can regain control and reduce the risk of future attacks.
Remember, knowledge is power—staying informed about potential threats and knowing how to respond effectively can make all the difference in safeguarding yourself against phishing attacks.
How is AI Changing the Landscape of Phishing Attacks?
Artificial Intelligence (AI) has revolutionized many aspects of our lives, and cybersecurity is no exception. As AI technology advances, it is also being leveraged by cybercriminals to create more sophisticated and targeted phishing attacks. Understanding how AI is changing the landscape of phishing attacks is crucial for staying ahead of these evolving threats.
The Role of AI in Crafting Sophisticated Phishing Schemes
AI algorithms can analyze vast amounts of data to create highly personalized phishing messages that are more likely to fool victims. By scraping information from social media profiles, public records, and data breaches, attackers can craft messages that appear to come from trusted sources and are tailored to individual interests and behaviors.
I recently came across an example of an AI-generated phishing email that was so convincing that it fooled even seasoned cybersecurity experts. The email used the recipient’s name, job title, and company information to create a sense of legitimacy. It also referenced a recent project the person had worked on, making it seem like a genuine communication from a colleague.
Automating Phishing Campaigns with AI
AI can also be used to automate the process of sending out phishing messages at scale. Attackers can use AI-powered tools to generate thousands of unique emails, each with a slightly different message or sender address. This makes it harder for security systems to detect and block these attacks.
I’ve seen reports of phishing campaigns that use AI to automatically generate new malicious domains and email addresses in real-time. As soon as one is blocked, another takes its place, creating an endless cycle of attacks.
Evading Detection with AI-Powered Malware
AI is also being used to create malware that can evade detection by traditional security measures. Malware powered by AI can adapt its behavior and code to bypass antivirus software and firewalls. It can also learn from its environment and find new ways to infiltrate systems and networks. I remember reading about a case where an organization was hit by an AI-driven malware attack that went undetected for months. The malware was able to blend in with normal network traffic and slowly gather sensitive data without raising any red flags.
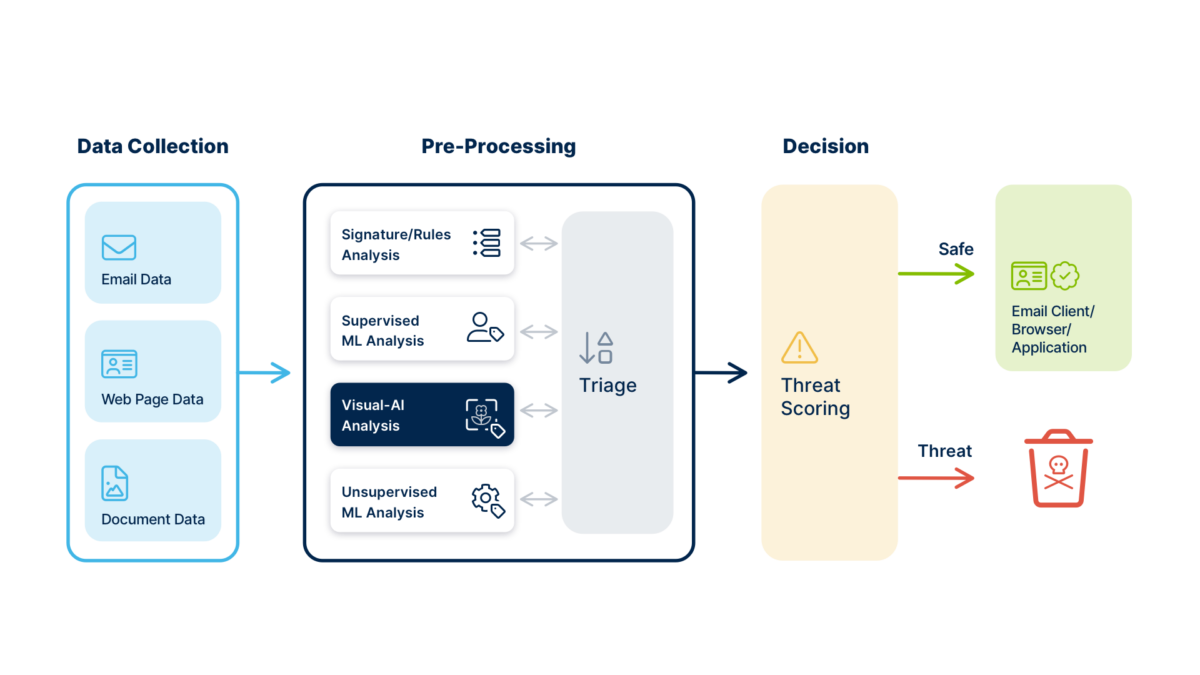
Countermeasures Using AI for Detection and Prevention
While AI poses a significant threat in the hands of cybercriminals, it can also be used as a powerful tool for detecting and preventing phishing attacks. Security researchers are developing AI-based systems that can analyze email content, sender behavior, and network traffic patterns to identify potential threats in real-time.
I’ve seen AI-powered email filters that can detect phishing messages with a high degree of accuracy, even if they are highly personalized or use advanced social engineering tactics. These systems learn from past attacks and continuously adapt to new threats, making them an effective line of defense against evolving phishing schemes.
As AI technology continues to advance, it is clear that the landscape of phishing attacks will continue to evolve. Cybercriminals will likely leverage AI to create more sophisticated and targeted attacks, making it harder for individuals and organizations to detect and prevent them.
However, the same technology that enables these attacks can also be used to defend against them. By investing in AI-powered security solutions and staying informed about the latest threats, we can stay one step ahead of the attackers and protect ourselves from the devastating consequences of phishing attacks.
What Are the Future Trends in Phishing Attacks?
As technology continues to evolve, so do the tactics employed by cybercriminals, particularly in the realm of phishing attacks. Understanding future trends in phishing can help individuals and organizations better prepare and protect themselves against these ever-evolving threats. In this section, we’ll explore some of the anticipated trends in phishing attacks and how they may impact users in the coming years.
Increased Use of Artificial Intelligence
As discussed earlier, AI is already being used to craft more sophisticated phishing schemes. Moving forward, we can expect cybercriminals to leverage AI even more extensively to automate and enhance their attacks. This could include:
- Hyper-Personalization: AI algorithms will analyze vast amounts of data to create highly personalized phishing messages that are difficult to distinguish from legitimate communications. The more tailored the message, the greater the chance of success. I’ve seen examples where attackers use AI to generate messages that reference recent events or personal details about the target, making them seem incredibly convincing. For instance, an email might mention a recent vacation or a shared interest in a specific topic.
- Adaptive Phishing Techniques: AI can enable attackers to adapt their strategies based on real-time feedback. If a particular phishing email is blocked or reported, AI can quickly analyze why it failed and adjust future attempts accordingly.
Rise of Voice Phishing (Vishing)
With the increasing sophistication of voice recognition technology, we can expect a rise in voice phishing (vishing) attacks. Attackers may use AI-generated voice simulations to impersonate trusted individuals over the phone, making it harder for victims to detect fraud. Imagine receiving a call from someone who sounds exactly like your bank’s representative, complete with their tone and mannerisms. This level of realism could make it challenging for individuals to discern whether they are speaking with a legitimate source or a scammer.
Phishing via Social Media and Messaging Apps
As social media platforms and messaging apps become more popular for communication, cybercriminals are likely to exploit these channels for phishing attacks. We may see an increase in scams that involve:
- Direct Messages: Attackers could send direct messages on platforms like Facebook, Instagram, or WhatsApp that appear to come from friends or trusted contacts, urging users to click on malicious links. I’ve noticed an uptick in messages from acquaintances claiming they’ve won prizes or need help with urgent issues. These scams often lead to phishing sites designed to steal personal information.
- Fake Accounts: Cybercriminals may create fake accounts that closely resemble legitimate businesses or influencers to trick users into providing sensitive information or clicking on harmful links.
Mobile Phishing Attacks
With more people accessing the internet via mobile devices, mobile phishing (or smishing) is expected to grow significantly. Attackers may use SMS messages to deliver phishing links that lead users to fake websites designed to harvest personal information. I’ve received text messages claiming to be from delivery services or banks asking me to verify my account details through a link. These messages often include urgent language designed to provoke immediate action without careful consideration.
Increased Focus on Data Breaches
As data breaches continue to make headlines, attackers may increasingly target organizations with weak security measures. Once they gain access to sensitive data, they can use this information for highly targeted phishing attacks against employees or customers. For example, if an organization suffers a data breach that exposes employee email addresses and job titles, attackers can craft convincing spear-phishing emails tailored specifically for those individuals.
The future of phishing attacks is likely to be characterized by increased sophistication and adaptability as cybercriminals leverage emerging technologies like AI and exploit new communication channels. By staying informed about these trends and implementing robust cybersecurity measures, individuals and organizations can better protect themselves against the evolving threat landscape. Awareness is key; understanding how these trends may manifest allows us to remain vigilant and proactive in our efforts to combat phishing attacks effectively.
Final Thoughts: Staying Vigilant Against Phishing Attacks
As we’ve explored throughout this article, phishing attacks are a persistent and evolving threat that can have devastating consequences for individuals and organizations alike. However, by staying informed, implementing effective security measures, and maintaining a vigilant mindset, we can significantly reduce our risk of falling victim to these malicious schemes.
Recap of Key Points
In this comprehensive guide, we’ve covered the fundamentals of understanding phishing attacks, including:
- The definition and evolution of phishing
- The mechanisms used by attackers and the role of social engineering
- Common signs of phishing scams and techniques used by cybercriminals
- The potential consequences of falling victim to a phishing attack
- Effective phishing prevention tips for individuals and organizations
- Steps to take if you suspect you’ve been targeted by a phishing attempt
- The impact of emerging technologies like AI on the future of phishing attacks
By understanding these key points and applying the strategies outlined in this article, you can better protect yourself and your organization from the dangers of phishing.
The Importance of Ongoing Education and Vigilance
Staying vigilant against phishing attacks requires a proactive and continuous approach. Cybercriminals are constantly evolving their tactics, so it’s crucial to stay informed about the latest threats and best practices for prevention. I recommend regularly reviewing cybersecurity resources, participating in online forums, and attending workshops or webinars on the topic.
By continuously educating yourself and your team, you can stay ahead of the curve and maintain a strong defense against phishing attacks. It’s also essential to foster a culture of vigilance within your organization. Encourage employees to report suspicious emails or messages, and provide regular training sessions to reinforce the importance of cybersecurity best practices.
In conclusion, phishing attacks pose a significant threat in today’s digital landscape, but by understanding the risks and taking proactive steps to mitigate them, we can protect ourselves and our organizations from the devastating consequences of these malicious schemes. Remember, staying vigilant is a continuous process, and by working together as a community, we can create a safer online environment for everyone.
Frequently Asked Questions (F.A.Q.s)
- What is the most common type of phishing attack?
- The most common type of phishing attack is email phishing, where attackers send fraudulent emails that appear to come from trusted sources to trick individuals into revealing sensitive information.
- How can I tell if an email is a phishing attempt?
- Look for red flags such as poor grammar, generic greetings, suspicious links or attachments, and urgent calls to action. Always verify the sender’s email address.
- What should I do if I clicked on a phishing link?
- Immediately disconnect from the internet, change your passwords for affected accounts, monitor your financial statements for unauthorized transactions, and run a security scan on your device.
- Are there tools available to help prevent phishing attacks?
- Yes, many security software solutions offer anti-phishing features. Additionally, browser extensions and email filters can help detect and block phishing attempts.
- How do attackers gather information for spear phishing?
- Attackers often gather information through social media profiles, data breaches, and public records to craft personalized messages that appear legitimate.
- What are some examples of successful phishing scams?
- Notable examples include the 2016 Democratic National Committee email breach and various scams impersonating tech support from major companies like Microsoft.
- Can social media be used for phishing attacks?
- Absolutely! Cybercriminals often use social media platforms to send direct messages or create fake accounts to trick users into providing personal information.
- How can organizations train employees to recognize phishing?
- Organizations can implement regular training sessions that include real-life examples, simulated phishing attempts, and best practices for identifying suspicious communications.
- What legal actions can be taken against phishers?
- Phishing is illegal, and victims can report incidents to law enforcement agencies. Authorities may investigate and pursue criminal charges against the perpetrators.
- Is it safe to use public Wi-Fi when accessing sensitive information?
- Public Wi-Fi networks are generally not secure. It’s advisable to avoid accessing sensitive accounts or use a Virtual Private Network (VPN) if you must connect to public Wi-Fi.


